Matrix-Themed OpenClaw Agent Operating System
A public-safe architecture overview for a human-controlled, multi-agent AI operations platform designed around separation of duties, security review, approval gates, workflow automation, and controlled execution.
What This Page Intentionally Does Not Reveal
This page describes the architecture, controls, and operating model without exposing sensitive implementation details. Private operational data has been intentionally omitted.
No Secrets
No API keys, tokens, passwords, credentials, session values, secrets, private environment variables, or authentication material are included.
No Private Infrastructure
No private IP addresses, hostnames, usernames, raw file paths, admin access instructions, or private implementation-specific endpoints are included.
No Private Personal Data
No private family details, private accounts, private contact details, customer information, or sensitive business records are included.
AI Operations Without Handing the Keys to One Overpowered Bot
This project documents a Matrix-inspired OpenClaw multi-agent operating system where the human operator remains the final authority, Trinity acts as the primary orchestrator, and specialized agents handle security, communications, execution, research, audit, scheduling, memory, business growth, and workflow design.
The core problem this architecture solves is the risk of giving a single autonomous AI agent too much authority. OpenClaw-style environments are powerful because they can use tools, spawn sessions, manage files, communicate, run scheduled jobs, access APIs, and coordinate external systems. That flexibility is useful, but it also creates risk when planning, execution, communication, auditing, and administration collapse into one agent.
This design breaks those responsibilities apart. Edwin functions as Neo: the human decision-maker, owner, and final authority. Trinity is the main orchestration layer. Morpheus handles cybersecurity review. Link is the only outbound communications gateway. Keymaker is the privileged admin and secrets executor. Agent Smith manages disposable worker agents. Business-growth agents support revenue, marketing, proposals, CRM, analytics, and customer success without bypassing communication or security controls.

Why This Architecture Exists
The starting point was practical: OpenClaw provides a flexible AI-agent runtime, but that flexibility can feel like a frontier environment where too much is possible too quickly. A powerful root agent can access tools, spawn sessions, schedule work, read and write files, communicate through plugins, and coordinate external services.
Rather than treat the root agent as an all-powerful assistant, the system was redesigned around separation of concerns. Trinity remains the primary interface, but other specialized agents handle security, communications, reporting, scheduling, testing, configuration drafting, knowledge hygiene, lead generation, and business intelligence.
The Matrix theme gives the system a memorable operating language. Edwin is Neo, the human in control. Trinity is the trusted orchestrator. Morpheus protects the system through cybersecurity review. Link controls outbound communication. Keymaker protects privileged access. Agent Smith manages disposable workers. The theme is fun, but the architecture underneath is serious: security, approvals, least privilege, and repeatable operations.
What This Solves
Single-Agent Overreach
Planning, execution, communication, security review, privileged administration, and audit functions are separated into clearly scoped agent roles.
Unsafe Outbound Messaging
All outbound communications are routed through one communications gateway so other agents cannot accidentally disclose information or send unapproved messages.
Privilege Sprawl
Privileged actions are isolated behind Keymaker and require a hard approval chain before execution.
Uncontrolled Task Execution
Disposable worker agents receive task-scoped assignments, minimum necessary context, limited tools, and reset after completion.
Manual Workflow Buildout
Agents help design, test, document, and maintain repeatable n8n workflows instead of relying on manual one-off automation work.
Poor Visibility
Monitoring, reporting, logging, scheduling, and business intelligence functions make activity measurable, explainable, and reviewable.
Working with AI for Protection
The system assumes that powerful agent tools create real attack surfaces: prompt injection, unsafe plugin use, accidental data leakage, excessive context exposure, unauthorized outbound communication, credential mishandling, runaway scheduled jobs, and unreviewed system changes.
Morpheus, Seraph, Cypher, Sati, Link, and Keymaker exist to reduce those risks by forcing work through defined roles, review points, and approval paths.

Self-Hosted AI Operations Layer
The architecture runs as a self-hosted AI operations layer rather than a purely cloud-hosted assistant. It uses an isolated virtualized environment, an Ubuntu server base, OpenClaw as a Node.js-based multi-agent gateway, local model options, cloud AI services, workflow automation, controlled communication channels, and monitored support components.
Agent workspaces are treated as part of the behavioral control surface. Each agent can have scoped tool permissions, sandboxing boundaries, identity notes, memory instructions, and role-specific operating guidance. The design assumes that how agents are organized matters as much as what model powers them.
| Layer | Component | Purpose |
|---|---|---|
| Compute | Self-hosted virtual machine running Ubuntu | Provides an isolated environment for the OpenClaw runtime. |
| Agent Runtime | OpenClaw | Provides the multi-agent gateway, workspace environment, tool surface, and agent coordination layer. |
| Local AI | Local model tooling | Supports local inference, experimentation, cost control, and model diversity. |
| Cloud AI | Cloud model providers | Used selectively by role, cost, reasoning complexity, and risk profile. |
| Communication | Approved messaging and email channels | Supports approvals, alerts, drafts, and outbound messaging through Link. |
| Workflow | n8n | Repeatable workflow layer designed by agents and deployed through review and approval. |
| Search | Provider-based web search | Supports research and intelligence gathering without hardcoding one source. |
| Network Support | Read-only monitoring components | Provides controlled visibility without granting broad system control. |
| Configuration Workflow | Conversational coding and controlled administration | Allows setup and troubleshooting through a documented, review-friendly process. |
Model Intelligence Is Not Authority
A more capable model does not automatically receive more permission. Permission is based on role, risk, review, and approval. The human operator remains accountable for sensitive decisions, while agents are constrained to defined responsibilities.
Trinity may coordinate, but Trinity does not own every permission and does not bypass specialist review. Link is the only agent allowed to send outbound communications. Keymaker is the only privileged admin and secrets executor. Agent Smith is the only manager of disposable worker agents. High-risk actions are reviewed by Morpheus and approved by the human operator before execution.

Human-in-the-Loop Approval
The human decision-maker stays in control of sensitive, external, privileged, and high-risk actions. Agents can propose, prepare, analyze, and test, but the final authority remains human.
- 1 Human ApprovalSensitive, external, privileged, or high-risk actions require explicit approval before execution.
- 2 Single Communications GatewayAll outbound communication routes through Link. Other agents may draft or request messages, but they do not send.
- 3 Privileged Admin RedlinePrivileged changes must follow the approved chain: Trinity → Morpheus → Link → Human Approval → Keymaker.
- 4 Disposable ExecutionAgent Smith assigns one scoped task to one worker. Workers do not self-direct, communicate externally, or retain broad context.
- 5 Context MinimizationSati limits what each agent receives and helps prevent unnecessary memory exposure.
- 6 Testing Before ActivationSeraph validates prompts, workflows, and configuration changes before they go live.
- 7 AuditabilityReports, logs, approval summaries, and completion notices help preserve traceability and accountability.
Capability and Authority Are Separate
Different model classes are used for different work. Routine, structured, repetitive, or narrow-scope agents can use smaller models to keep cost and latency low. Higher-risk reasoning, complex architecture, strategy, or security-sensitive decisions can be escalated to stronger models when needed. Local models support experimentation, offline workflows, privacy-aware testing, and model comparison.
The model strategy is not just about cost. It reinforces separation of duties. An agent can be intelligent without being authoritative. A small model can be safe when it has narrow scope and limited tools. A powerful model can still be dangerous if it has broad permissions. The architecture separates model capability from system authority.
| Model Class | Use | Examples |
|---|---|---|
| Small / Efficient Models | Default persistent agent duties | Routine reporting, structured tasks, lead processing, CRM hygiene, scheduling, and knowledge organization. |
| Mid-Tier Models | Escalated reasoning where needed | Configuration design, research synthesis, deeper review, and heavier drafting. |
| Flagship Models | High-risk or high-complexity escalation | Security reviews, architecture decisions, complex debugging, strategy, and public-facing claims review. |
| Local Models | Local experimentation and flexible inference | Sandboxed tests, private drafts, offline experiments, and alternative model comparisons. |
From Request to Reviewable Execution
The human operator works primarily through Trinity. Trinity evaluates whether a request is simple, project-based, workflow-driven, security-sensitive, communication-related, reporting-related, or administrative. Trinity does not try to do everything directly. Trinity coordinates the right agents.
For project-like work, Trinity convenes the relevant agent team. Oracle may evaluate strategy. Architect may design structure. Morpheus may identify risk. Seraph may create a validation plan. Councillor may review business language. The Analyst may define measurement. Link may prepare approval messages. Trinity consolidates the discussion and returns with a practical plan.
The Orchestrator Pattern
Trinity turns goals into coordinated work. The orchestrator does not become the executor of everything; it delegates, consolidates, escalates, and reports.
The Matrix-Inspired Team
The agent architecture is organized into layers: human control, orchestration, security and controls, privileged execution, worker execution, operations, knowledge, and business growth. The Matrix naming convention makes the system easier to understand and operate, while the boundaries underneath keep the system controlled.
Edwin / Neo — Human Authority
Human decision-maker, admin, and final authority. Approves sensitive actions, sets direction, owns risk, and remains accountable for outcomes.

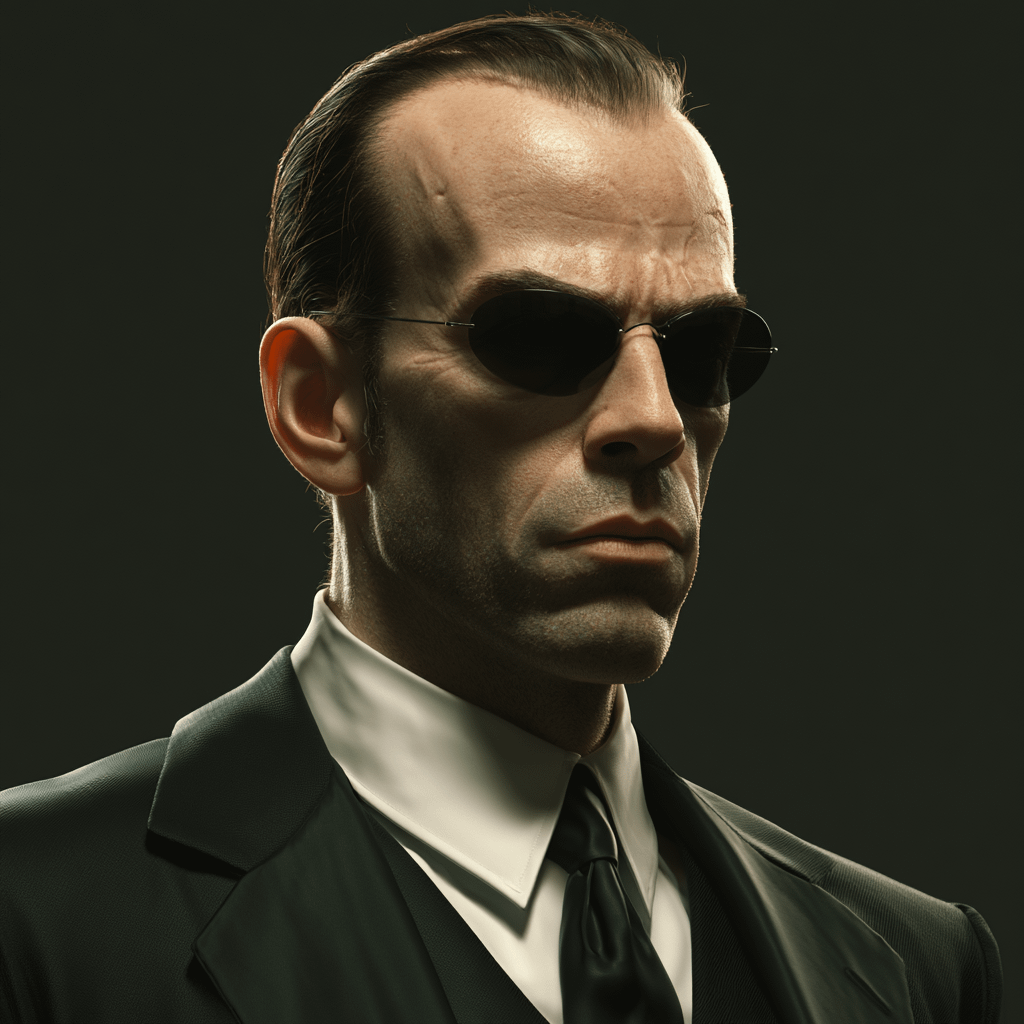
Trinity — Orchestrator / Manager
Primary interface. Plans, delegates, coordinates agents, consolidates recommendations, and manages projects without becoming a reckless executor.
Morpheus — Cybersecurity Agent
Reviews risks, permissions, prompt-injection exposure, tool access, agent changes, cron jobs, communication paths, and system behavior.
Link — Communication Agent
Single outbound communications gateway. Handles approval messages, professional email drafts, alerts, reports, and approved delivery.
Keymaker — Privileged Admin / Secrets Executor
Executes privileged or secrets-related actions only after the hard approval chain. Verifies authorization, masks sensitive values, logs actions, and reports completion.
Agent Smith — Disposable Worker Manager
Queues approved tasks, assigns one task to one worker, enforces concurrency limits, collects reports, and resets workers after completion.
Tank — System Operations / Runtime Support
Observes runtime health, diagnoses operational issues, prepares runbooks, and recommends admin actions without becoming the admin executor.
Oracle — Strategy / Decision Support
Analyzes tradeoffs, second-order effects, strategic decisions, and phased implementation paths before major architectural, business, or workflow decisions.

Niobe — Research / Intelligence Gathering
Conducts structured research, organizes evidence, verifies facts, and prepares research packets for business and operational decisions.
Seraph — QA / Testing / Validation
Tests prompts, workflows, configs, and agent behavior before activation. Produces clear validation outcomes such as pass, fail, needs revision, or blocked.
Architect — Configuration / Agent Design
Drafts agent definitions, workflow designs, configuration plans, workspace structures, and implementation proposals.
Councillor — Compliance / Language Review
Reviews business language, external-facing copy, proposals, outreach drafts, and compliance-sensitive wording. Does not act as legal counsel.
Cypher — Red-Team / Prompt-Injection Tester
Safely tests whether agents, prompts, approval chains, and tool boundaries can be bypassed using mock attacks and controlled simulations.
Dozer — Scheduler / Cron Coordinator
Manages recurring-workflow proposals, schedule registry, job cadence, failure behavior, and cron health to avoid schedule sprawl.

Sati — Memory / Knowledge Librarian
Organizes durable knowledge, context packets, memory hygiene, sensitivity categories, and context minimization.
Disposable Worker Pool — Brown, Jones, Jackson, Johnson, Thompson
Task-scoped workers. Each receives one assignment, uses minimum required context and tools, reports back, and resets or terminates.
High-Risk Work Must Pause
Approval flows are the backbone of the system. The goal is not to slow everything down. The goal is to prevent powerful agents from quietly accumulating authority. Low-risk work can move quickly. High-risk work must pause, summarize, and request approval.
The most important redline is the Keymaker chain. Trinity may not contact Keymaker directly for privileged work. Any admin, secrets, credential, API-key, environment variable, gateway, service restart, file permission, or elevated system change must follow a controlled route.
| Approval Type | Required Flow |
|---|---|
| General Project Approval | Trinity convenes relevant agents, consolidates a plan, and Link requests approval if required. |
| Agent Creation or Modification | Architect designs, Morpheus reviews security, Seraph validates, and Link requests approval. |
| Outbound Communication | All outbound communication goes through Link. Other agents may draft or request but may not send. |
| Privileged Admin or Secrets Action | Must follow Trinity → Morpheus → Link → Human Approval → Keymaker. No direct Trinity-to-Keymaker requests. |
| Disposable Worker Execution | Trinity requests an approved task. Agent Smith assigns a worker, collects the report, and resets the worker. |
| Recurring Automation | Dozer drafts cadence, Morpheus reviews risk, Seraph validates, Link requests approval, and Keymaker deploys if privileged. |
| Database or Report Access | The Analyst uses read-only access through approved views. Keymaker provisions access only after review and approval. |
No Single Agent Should Plan, Approve, Execute, Communicate, and Audit the Same Action
Separation of duties prevents a single agent from becoming too powerful. This system explicitly avoids allowing one agent to control every stage of the same action.
| Control Area | Primary Agent(s) | Boundary |
|---|---|---|
| Plan | Trinity, Oracle, Architect, Merovingian | Plans require review when permissions, communications, security, or admin actions are involved. |
| Security Review | Morpheus | Reviews risk independently and does not execute privileged changes. |
| Communication | Link | Only agent allowed to send external messages. |
| Privileged Execution | Keymaker | Executes only approved admin or secrets actions. |
| Routine Execution | Agent Smith and disposable workers | Task-scoped workers do not self-assign, communicate externally, or retain broad context. |
| Testing | Seraph | Validates behavior before changes go live. |
| Scheduling | Dozer | Coordinates schedules but does not activate high-risk cron jobs without review. |
| Memory | Sati | Provides minimum necessary context and avoids raw secrets in memory. |
| Reporting | The Analyst | Uses read-only reporting access and does not modify production data. |
Turning Agent Work into Durable Infrastructure
A major operating shift is that repeatable workflows are designed and maintained as durable infrastructure. A one-off request can become a managed n8n workflow when it has a predictable trigger, repeatable steps, defined inputs, clear outputs, measurable success criteria, and a known owner.
Agents should not create random automations. Each flow should have a purpose, owner, trigger, data-access requirements, communication behavior, failure behavior, audit trail, rollback plan, and retirement condition.
- 1 RequestThe human operator asks Trinity for a business or operations outcome.
- 2 PlanTrinity defines the goal and convenes the right agents.
- 3 DesignArchitect drafts the n8n workflow and required components.
- 4 Risk ReviewMorpheus reviews permissions, data movement, tool access, and security concerns.
- 5 TestSeraph validates with mock data or sandbox execution.
- 6 ApprovalLink sends a clear approval request to the human operator.
- 7 DeployKeymaker performs privileged deployment steps if needed.
- 8 ScheduleDozer registers cadence and failure behavior.
- 9 DocumentSati records purpose, context, and operating notes.
- 10 MeasureThe Analyst reports performance, bottlenecks, and operational value.
Monitoring Turns Automation into Operations
Workflows become safer when they are measured, reviewed, scheduled, documented, and retired when no longer useful. The Analyst, Dozer, Tank, Morpheus, and Sati help keep automation visible.
Who Is Responsible, Accountable, Supporting, Consulted, and Informed
RASCI helps keep ownership clear. R means Responsible, A means Accountable, S means Support, C means Consulted, and I means Informed. The human operator remains accountable for sensitive decisions, while Trinity remains accountable for orchestration.
| Workstream | R | A | S | C | I |
|---|---|---|---|---|---|
| Project Intake and Planning | Trinity | Human / Trinity | Oracle, Architect | Morpheus, The Analyst | Link, Sati |
| Agent Creation / Modification | Architect, Trinity | Human | Seraph | Morpheus, Sati | Link, Agent Smith |
| Cybersecurity Review | Morpheus | Human | Cypher, Seraph | Trinity, Tank | Link |
| Outbound Communication | Link | Human | Councillor, Rama, Switch | Morpheus when sensitive | Trinity |
| Privileged Admin / Secrets Change | Keymaker | Human | Tank | Morpheus | Trinity, Link |
| Disposable Task Execution | Agent Smith + Worker Pool | Trinity | Seraph if testing needed | Morpheus if risk | Human |
| Runtime Health Review | Tank | Trinity | Dozer, monitoring patterns | Morpheus | Human |
| Scheduled Work / Cron | Dozer | Trinity / Human | Architect | Morpheus, Seraph | Link |
| Memory and Context Hygiene | Sati | Trinity | Morpheus | Human | Relevant agents |
| Business Research | Niobe | Trinity | Apoc, The Analyst | Oracle | Human |
| Revenue Strategy | Merovingian | Human / Trinity | Oracle, The Analyst | Councillor | Link |
| Lead Generation | Apoc | Merovingian | Niobe, Vector | Councillor | Trinity |
| Marketing and SEO | Persephone | Merovingian / Trinity | Mouse, The Analyst | Councillor | Human |
| n8n Workflow Buildout | Architect, Seraph, Dozer | Trinity / Human | Keymaker if deployment needed | Morpheus | Sati, The Analyst |
Commercial Usefulness Without Bypassing Controls
The control layer keeps the system safe. The business growth layer makes it commercially useful. These agents help with revenue strategy, lead generation, marketing, sales development, proposals, CRM hygiene, customer success, and analytics while still respecting the same communication, review, and approval boundaries.
Daily Coordination and Business Reviews
Business agents can meet around strategy, pipeline health, reporting, and operational priorities, but outbound communication remains controlled through Link and sensitive language can be reviewed by Councillor.
Merovingian — Revenue Strategy
Owns revenue strategy, target markets, sales motion, pricing logic, offer prioritization, and pipeline strategy.
Apoc — Lead Generation
Builds targeted lead lists and prospect pools for websites, automation services, platform sales, and business opportunities.
Switch — Sales Development
Turns raw leads into qualified opportunities, prepares outreach angles, tracks objections, and recommends follow-up.
Persephone — Marketing and SEO
Owns SEO strategy, content themes, landing page strategy, keyword opportunities, and inbound growth planning.
Mouse — Creative and UX
Handles visual direction, UX audits, landing page structure, wireframes, conversion flow, and brand consistency.
Rama — Proposal and Offer Packaging
Builds proposals, service packages, pricing tiers, scope outlines, and client-ready offer structures.
Vector — CRM and Pipeline Operations
Maintains pipeline hygiene, stages, duplicates, source attribution, follow-up dates, and CRM data quality.
Zee — Customer Success
Tracks onboarding, check-ins, support needs, renewals, satisfaction, and relationship health.
The Analyst — BI and Growth Analytics
Builds reports, dashboards, KPI views, conversion analysis, growth metrics, and business intelligence outputs through read-only access patterns.
Recurring Work Without Background Chaos
The system supports both on-demand projects and recurring work. Recurring jobs must be intentionally designed and registered. Dozer manages recurring-workflow coordination so scheduled work remains understandable and does not become background chaos.
Cadence is based on risk and value. Security reviews may run daily or after major changes. Monitoring checks may run frequently. Lead-generation research may run on an approved schedule. BI reports may run weekly or monthly. Communication approvals should happen only when there is something meaningful to send.
Hourly
Queue checks, selected monitoring, approved operational health checks, and time-sensitive workflow activity.
Daily
Security summary, log review, task backlog review, lead or pipeline summary, and workflow health checks.
Weekly
Business performance report, sales pipeline review, SEO and content planning, and customer success check-ins.
Monthly
Executive operating review, cost review, model usage review, security posture review, and workflow cleanup.
On Demand
Projects, proposals, privileged changes, communication approvals, new workflows, and new agent designs.
Continuous Improvement
Agent prompts, workflow templates, approval paths, dashboards, and controls are reviewed as the system matures.
Designed to Be Publishable Without Exposing the System
This page is designed to describe the architecture, what it solves, and how the agents work together without revealing sensitive operational details. Screenshots, diagrams, and technical notes should always be reviewed for hidden hostnames, emails, usernames, API tokens, local paths, internal channel names, or private customer and business data before publishing.
Future Enhancements
- Stronger role-based permissions
- Formal policy-as-code
- Signed approval tokens
- Centralized audit logs
- Database reporting views
- Model cost dashboards
- Automated regression tests for agent prompts
- Staging environment for n8n workflows
- Public demo mode using synthetic data only
Operating Principles to Preserve
- Create public demos with synthetic data only
- Maintain security review checklists for new tools
- Use database views for reporting where possible
- Track model cost, usage, failures, and approval bottlenecks
- Version control agent definitions and workflow templates
- Run Cypher and Seraph tests before publishing workflows
- Keep Link as the only sender as new channels are added
- Keep Keymaker isolated behind the hard approval chain
- Document workflows with owner, trigger, failure behavior, and retirement rules
Closing Summary
This Matrix-themed OpenClaw architecture is a practical experiment in building AI operations with control, clarity, and security. It is not designed to replace human judgment. It is designed to coordinate useful work, enforce boundaries, preserve approval, and turn AI from a single assistant into a structured operating system.
The long-term principle is simple: Trinity remains the orchestrator, specialist agents stay in their lanes, sensitive work requires review, and the human operator remains the final authority.